To secure consumer data, organizations need to make sure that their networks are updated and protected against any malicious activity. The wide accessibility of the internet around the globe has made it easy for hackers to intrude into an organization’s system in an unethical manner and compromise their security controls to fulfill their harmful goals.

The complexity of the software being built and that billions of devices are connected with them through the internet, makes them vulnerable to security threats. Organizations that possess huge chunks of data can be in danger of being exploited by intruders who gain access to critical data, subsequently causing them to lose customers and money. For businesses to remain safe, and sustainable in the face of competition, it is necessary to use a comprehensive approach to foolproofing their systems. Various standardized security methods are available. One such specialized technique is penetration testing, which aims to detect any loophole in the system through which an attacker can gain access and steal critical data, which ultimately causes businesses to suffer monetary losses and lose customers to competitors.
An Introduction to Penetration Testing
Penetration testing is comprehensively performed over a fully-functional system’s software and hardware. This technique helps identify any weak points in the system that an attacker may be able to exploit.
In addition to minimizing the risk of compromise to the system, the system’s configuration is also analyzed by validating checks on software and hardware. Penetration testing is also known as ethical hacking and can be performed both manually and through automation. To achieve the goals of pen-testing efficiently, various scenarios are designed to emulate breaking into the system to evaluate expected behavior for accurate results.
Why do we perform Penetration Testing?
As discussed initially, penetration testing carried out in a controlled environment where potential loopholes are identified and eliminated before attackers exploit them. If any loophole remains there, the attacker can gain access to the system and can utilize the data for malicious activities.
Pen-Testing Requirements: The Five Rs
Whenever organizations plan to carry out penetration testing in a controlled environment, the requirements should be realistic and reliable because the ethical hacker will simulate an actual activity where the system may actually be compromised. Hence, employee privacy rights need to be taken into consideration before performing this kind of activity. There are five such requirements of pen-testing, which should be fulfilled before pen-testing begins.
- Respect: Everyone associated with the system should be treated with respect during the execution of pen-testing, and should not be pressurized or made to feel uncomfortable.
- Restriction: People should behave in a normal manner, with no change from the way they act in their everyday lives.
- Reliable: Pen-testing should be reliable but not cause any slacking-off from the company’s routine work.
- Repeatable: Similar to other testing methods, pen-testing is executed multiple times for precise results. When the environment does not change, the results should remain the same.
- Reportable: It is essential to monitor and improve the process to increase effectiveness for the future. A log should be made for every important action, and the test results should be arranged in a meaningful order to help with decision making.
Types of Penetration Testing
In practice, the following types are those most commonly followed:
Black Box Testing: With black box testing, we have an executable code of the system but are unaware of the internal workings and environment. We provide input data and analyze the generated result and compare it with the expected output.
White Box Testing: With white box testing, the tester possesses complete information about the system. Experts need to analyze the code step by step to understand the functioning of the system, and then based on their knowledge, prioritize their test cases to identify vulnerabilities at all levels.
Phases in Penetration Testing
- Information Gathering: When testing a web application, it is necessary to gather all the required information related to the server beforehand. In this phase, we need to make sure what the right domain is and how many subdomains are linked to the parent’s domain, as well as if there is any firewall setup for the particular server or not. There are many tools available which detect the presence of a firewall such as WAFWOOF.
- Scanning: In this phase, scanning helps us to check which service is running on the server and at which port. For scanning, we use network scanner and mapping tools such as NMAP, and Paessler PRTG, or other available tools.
- Discovering Vulnerability: A penetration testing expert utilizes various tools to find any vulnerability in the system. These tools identify dangerous files and programs in the system and check for any loopholes.
- Exploitation: Once a vulnerability has been identified, the pen-tester’s next goal is to breach the system by taking it over through remote access of the server. For this purpose, experts usually use the tool, Metasploit.
- Reporting: In the last phase, as with all testing methods, a report is generated, and the future course of action is decided. The organization should make sure that reports do not fall into the wrong hands, hence becoming vulnerable to attacks. They must be kept well protected.
It is essential that the test results should be effective enough to suggest such ways to reduce potential vulnerabilities and to eliminate those which are identified during the testing process. This is how we primarily differentiate between penetration and security testing.
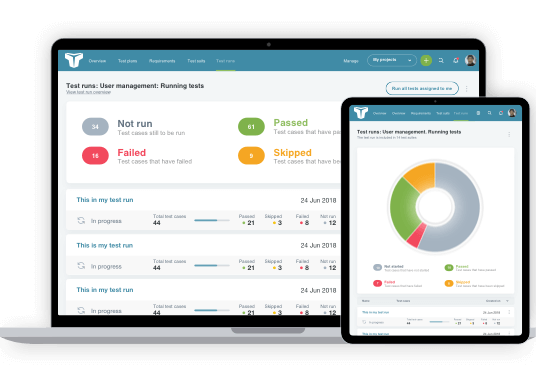
Penetration Testing Tools
There are many tools available for the purpose of penetration testing. No single tool can help an organization achieve its goal, but a set of various tools can support them in identifying loopholes in their system. Here, we list a few of the many tools available on the market:
Nmap: Often referred to as network mapper, nmap is a free and open source tool which allows experts to scan the system for vulnerabilities. Usually, with the help of NMAP, we are able to check which devices are connected with a particular system, scanning ports to determine whether they are open or closed, and detecting loopholes.
Nessue: It is one of the many tools available to help with identifying vulnerabilities in the system, including any malicious activity. The tool is managed by tenable and is available free to use for individuals or non-enterprise users.
Metasploit: One the important frameworks in penetration testing is Metasploit. With the help of this tool, we can develop, test, and exploit the system code. It is available both as open source and as a commercial version.
Benefits and Challenges
Penetration testing helps organizations to secure their systems from any attacker which tries to compromise their system. In short, we can say that pen-testing is an authorized way with which we can break the system by breaching the security with the attacker’s mindset.
Although there will always be room for improvement, challenges should be taken as opportunities to better the existing processes to achieve better quality. Few of the challenges are:
Limited Timeframe: Usually, when organizations are short on time, they usually compromise on the testing phase, which creates unnecessary pressure on the team. As penetration testing needs time, it is an unwelcome challenge to perform within the short time frame, which can leave the system vulnerable to attack.
Security: It is impossible to secure a system 100%, and the expertise of the professionals often determines the stability of the system.
Automation: A test automation framework can be established to reduce time and effort. Automation pen-testing can be performed with the help and guidance of expert testers.
Conclusion
Penetration testing can benefit organizations in many ways, including preventing monetary losses, preserving the brand reputation, compliance with statute rules and regulations, elimination of potential risks, and so on.
Penetration testing is a reliable method of identifying and eliminating any security loopholes which systems may face. It is essential to know that as a part of an organization’s security policy, pen-testing should be performed on a regular interval to improve a system’s stability.
About the writer
Syed Ali Imam
Syed Ali Imam is a Software Quality Assurance Engineer, currently working as a Functional Tester for Innovit Software Development in Australia.
All Syed Ali Imam's articles